I first encountered NSA Suite B encryption while studying how governments standardize cryptography across vast digital infrastructures. The topic initially seemed obscure, buried in technical specifications and federal guidelines. Yet the deeper I looked, the clearer it became that Suite B played a pivotal role in shaping how secure communication works today.
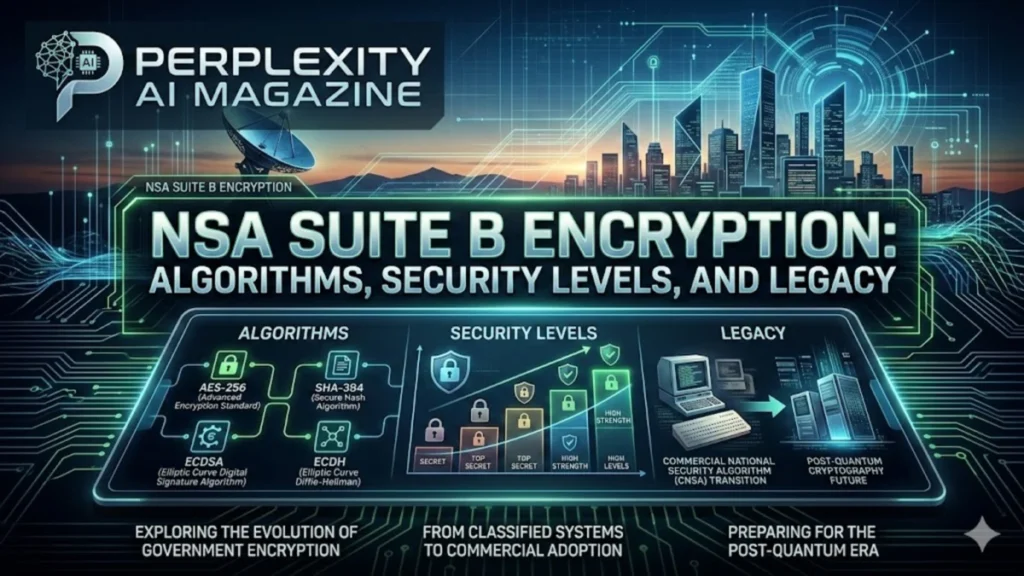
NSA Suite B cryptography was a standardized collection of algorithms introduced by the U.S. National Security Agency in 2005 to protect both classified and unclassified information. It combined well-known cryptographic tools such as the Advanced Encryption Standard (AES), elliptic-curve cryptography for key exchange and digital signatures, and secure hashing algorithms. The objective was straightforward but ambitious: provide interoperable, strong encryption across government and commercial systems.
Within a decade, Suite B had quietly influenced everything from military communications and satellite networks to enterprise VPN systems and operating systems. Technology companies integrated its algorithms into networking equipment, operating systems, and encryption libraries. For a time, it represented the cutting edge of government-approved cryptography.
But cryptography evolves as quickly as the threats against it. By 2015, the NSA announced that Suite B would be phased out and replaced by the Commercial National Security Algorithm (CNSA) suite. The reason was not a flaw in the algorithms themselves but a looming technological shift: quantum computing. The mathematical assumptions underpinning elliptic curve cryptography could eventually be broken by quantum algorithms.
Suite B therefore became both a milestone and a transition point in modern cryptography, marking the moment when governments began preparing seriously for a post-quantum world. – nsa suite b encryption.
The Origins of Suite B Cryptography
The creation of Suite B emerged from a practical challenge facing government agencies in the early 2000s. Secure communication systems across the United States government relied on numerous cryptographic standards, many of them proprietary or incompatible with commercial technologies.
I often think of Suite B as an attempt to simplify the cryptographic ecosystem. Instead of dozens of encryption schemes scattered across classified systems, the NSA proposed a unified framework built on algorithms already standardized by the National Institute of Standards and Technology (NIST).
Introduced at the 2005 RSA Conference, Suite B emphasized interoperability. Government agencies could deploy encryption using widely available algorithms, enabling easier integration with commercial technology vendors and software platforms.
Security experts saw this as a shift toward transparency. Bruce Schneier, a well-known cryptographer, noted in discussions about government cryptographic standards that public algorithms allow broader scrutiny and stronger trust because “cryptography that is open to analysis tends to be more secure than secret designs” (Schneier, 2015).
Suite B therefore represented more than a list of algorithms. It reflected a philosophy: adopt well-tested cryptographic methods that could scale across national security systems and commercial technology infrastructure.
Core Algorithms Inside the Suite
At its core, Suite B relied on four major categories of cryptographic primitives: symmetric encryption, digital signatures, key exchange, and hashing. These components formed a complete toolkit for secure communications.
The designers prioritized efficiency and strong mathematical foundations. Elliptic curve cryptography (ECC) played a central role because it offered comparable security to older algorithms like RSA while requiring significantly smaller key sizes.
This efficiency made ECC especially useful for bandwidth-constrained systems such as mobile devices, secure radios, and satellite communication links.
| Cryptographic Function | Algorithm Used | Typical Purpose |
|---|---|---|
| Symmetric Encryption | AES-128 / AES-256 | Protecting data confidentiality |
| Digital Signatures | ECDSA | Authenticating messages |
| Key Exchange | ECDH | Secure session key establishment |
| Hashing | SHA-256 / SHA-384 | Data integrity verification |
AES handled encryption of data both at rest and in transit. ECDH enabled secure key exchange without exposing secret keys. ECDSA provided digital signatures ensuring authenticity, while SHA-2 family hashing protected integrity.
Together, these algorithms formed a tightly integrated cryptographic stack used across government systems.
Security Levels and Classification Requirements
Suite B was also carefully structured to align cryptographic strength with national security classification levels. The NSA recognized that not all information required identical protection, so the suite defined separate parameters for Secret and Top Secret data.
In practice, the difference primarily involved larger key sizes and stronger hash functions for higher classifications.
| Classification Level | Encryption | Hashing | Key Exchange | Signatures |
|---|---|---|---|---|
| Secret | AES-128 | SHA-256 | 256-bit ECDH | 256-bit ECDSA |
| Top Secret | AES-256 | SHA-384 | 384-bit ECDH | 384-bit ECDSA |
This layered approach allowed agencies to deploy efficient encryption where possible while maintaining stronger protection for highly sensitive intelligence.
Matthew Green, a cryptography professor at Johns Hopkins University, has explained that elliptic curve cryptography “provides strong security with smaller keys and faster performance, which makes it attractive for constrained systems” (Green, 2014).
Suite B leveraged that efficiency to balance security and operational practicality.
Adoption Across Government and Industry
Once introduced, Suite B rapidly influenced both public and private technology ecosystems. Government agencies required vendors to support Suite B algorithms in order to qualify for certain contracts.
As a result, technology companies began integrating Suite B cryptography into operating systems, networking devices, and security appliances. – nsa suite b encryption.
Among the widely deployed implementations were:
- Microsoft Windows support for Suite B algorithms in IPsec policies beginning with Windows Vista and Windows Server 2008
- Cisco routers and switches supporting Suite B cipher suites for IPsec and IKEv2
- OpenSSL cryptographic library implementing elliptic curve support and AES-GCM encryption
- Red Hat Enterprise Linux configurations enabling Suite B-compliant TLS and IPsec
Enterprise middleware also followed suit. IBM MQ implemented Suite B-compliant TLS profiles that allowed secure communication between distributed systems.
The result was a rare alignment between government cryptographic policy and commercial technology products.
Why Elliptic Curve Cryptography Became Central
Elliptic curve cryptography represented one of the most significant shifts in modern cryptographic design. Unlike RSA, which depends on the difficulty of factoring large integers, ECC relies on the complexity of solving discrete logarithms on elliptic curves.
This difference dramatically reduces key size requirements.
For example, a 256-bit elliptic curve key offers security roughly equivalent to a 3072-bit RSA key. The smaller keys reduce computational load, which matters for devices with limited resources.
Whitfield Diffie, co-inventor of public-key cryptography, has observed that cryptographic efficiency often determines whether secure systems can be deployed widely, noting that “performance considerations shape real-world adoption just as much as theoretical strength” (Diffie & Landau, 2007).
Suite B embraced ECC precisely because it allowed secure communication on devices ranging from smartphones to military radios.
This efficiency advantage helped ECC become a cornerstone of modern internet security, including TLS encryption and secure messaging systems. – nsa suite b encryption.
The Quantum Threat That Changed Everything
Despite its strengths, Suite B faced an emerging threat that could not be solved simply by increasing key sizes.
Quantum computing introduced a new class of algorithms capable of solving mathematical problems that underpin classical cryptography.
Shor’s algorithm, proposed in 1994, demonstrated that sufficiently powerful quantum computers could break both RSA and elliptic curve cryptography by efficiently solving integer factorization and discrete logarithm problems.
For years this threat remained theoretical because practical quantum computers were far from capable of executing such attacks.
By the early 2010s, however, research progress began to accelerate. Governments and security agencies started considering the possibility that encrypted data intercepted today might be decrypted decades later when quantum hardware matures.
This “harvest now, decrypt later” threat prompted the NSA to reevaluate long-term cryptographic strategies.
The Birth of the CNSA Suite
In July 2015 the NSA announced a new cryptographic framework called the Commercial National Security Algorithm (CNSA) suite. This announcement effectively deprecated Suite B for new systems.
CNSA initially strengthened classical algorithms, increasing key sizes and preparing for a gradual transition toward quantum-resistant cryptography.
| Feature | Suite B | CNSA 1.0 | CNSA 2.0 |
|---|---|---|---|
| Primary Goal | Interoperable ECC security | Stronger classical security | Post-quantum readiness |
| Encryption | AES-128 / AES-256 | AES-256 | AES-256 |
| Key Exchange | ECDH | ECDH / RSA-3072 | ML-KEM |
| Signatures | ECDSA | ECDSA P-384 | ML-DSA |
| Quantum Resistance | No | Limited | Yes |
CNSA 2.0, announced in 2022, formally introduced post-quantum cryptographic algorithms such as ML-KEM (formerly CRYSTALS-Kyber) and ML-DSA (formerly CRYSTALS-Dilithium).
These lattice-based algorithms are designed to resist attacks from both classical and quantum computers.
Legacy Systems Still Using Suite B
Although Suite B has been retired for new deployments, many systems around the world still rely on its algorithms.
The reason is simple: cryptographic infrastructure evolves slowly. Government networks, satellite systems, and industrial control environments may operate for decades before being upgraded.
Suite B algorithms such as AES-256 and SHA-384 remain secure against classical attacks. The vulnerability arises only in a future where large-scale quantum computers become practical.
For that reason, some legacy systems continue to operate safely using Suite B-compliant cryptography while planning gradual migration toward CNSA 2.0 or post-quantum standards.
This transition process is expected to take many years.
The Role of Standards Organizations
The retirement of Suite B also illustrates how international cryptographic standards evolve.
The Internet Engineering Task Force (IETF) reclassified several Suite B RFC documents as “Historic” in 2017 through RFC 8423. This formal step signaled that the algorithms should not be used for new implementations.
Meanwhile, NIST launched a global competition in 2016 to identify post-quantum cryptographic algorithms capable of replacing RSA and ECC.
After several rounds of evaluation, NIST selected lattice-based algorithms such as CRYSTALS-Kyber and CRYSTALS-Dilithium as the foundation of future encryption standards.
These algorithms now form the backbone of CNSA 2.0.
The Broader Impact on Modern Cybersecurity
Suite B’s influence extended far beyond government networks. By encouraging the adoption of elliptic curve cryptography, it helped accelerate ECC deployment across the internet.
Today, ECC is widely used in HTTPS encryption, secure messaging apps, blockchain systems, and mobile devices.
The standard also demonstrated how government cryptographic policy can shape industry practices. Vendors seeking government contracts implemented Suite B algorithms, indirectly spreading ECC support across commercial software platforms.
Even though Suite B itself is no longer the recommended standard, its legacy persists in the cryptographic tools that underpin modern digital security.
Key Takeaways
- NSA Suite B cryptography was introduced in 2005 to standardize encryption across government and commercial systems.
- It relied heavily on elliptic curve cryptography for efficient and secure key exchange and digital signatures.
- Suite B defined separate algorithm strengths for Secret and Top Secret classified information.
- Major technology vendors integrated Suite B algorithms into operating systems, networking equipment, and security software.
- The NSA deprecated Suite B in 2015 due to concerns about future quantum computing threats.
- The CNSA suite replaced it, with CNSA 2.0 introducing post-quantum cryptographic algorithms.
- Suite B helped popularize elliptic curve cryptography, which remains widely used today.
Conclusion
I see Suite B as a pivotal chapter in the history of modern cryptography. It represented a moment when government security agencies aligned their standards with widely accepted academic algorithms, embracing transparency and interoperability.
For more than a decade, Suite B shaped the architecture of secure communications. Its algorithms protected classified intelligence networks, commercial infrastructure, and countless encrypted transactions.
Yet cryptography never stands still. The same scientific progress that enabled stronger encryption also revealed new vulnerabilities on the horizon. Quantum computing forced policymakers and researchers to rethink long-standing assumptions about digital security.
The transition from Suite B to the CNSA suite reflects that constant adaptation. Security standards must evolve not only to defend against current threats but also to anticipate future technological breakthroughs.
Suite B may now be classified as historic, but its influence continues to echo throughout the cryptographic systems that protect the modern digital world.
FAQs
What was NSA Suite B encryption used for?
Suite B defined a standardized set of cryptographic algorithms used to protect classified and unclassified government information. It supported secure communication, data encryption, authentication, and digital signatures across national security systems.
Why did the NSA replace Suite B?
The NSA replaced Suite B mainly due to concerns about quantum computing. Future quantum machines could break elliptic curve cryptography using Shor’s algorithm, making the suite unsuitable for long-term protection of classified data.
What algorithms were included in Suite B?
Suite B used AES for encryption, ECDH for key exchange, ECDSA for digital signatures, and SHA-256 or SHA-384 for hashing.
Is Suite B still secure today?
Yes, against classical computers. However, it is not considered future-proof because quantum computers could eventually break elliptic curve cryptography used within the suite.
What replaced Suite B?
The Commercial National Security Algorithm (CNSA) suite replaced Suite B. CNSA 2.0 introduces post-quantum cryptographic algorithms such as ML-KEM and ML-DSA.